Threats! Everywhere!

Out of curiosity, I enabled all of the threat detection and reporting systems on my home firewall. As it turns out, the home network is under siege.
The firewall is configured to report, but not take action, on all of the threats and attacks seen.
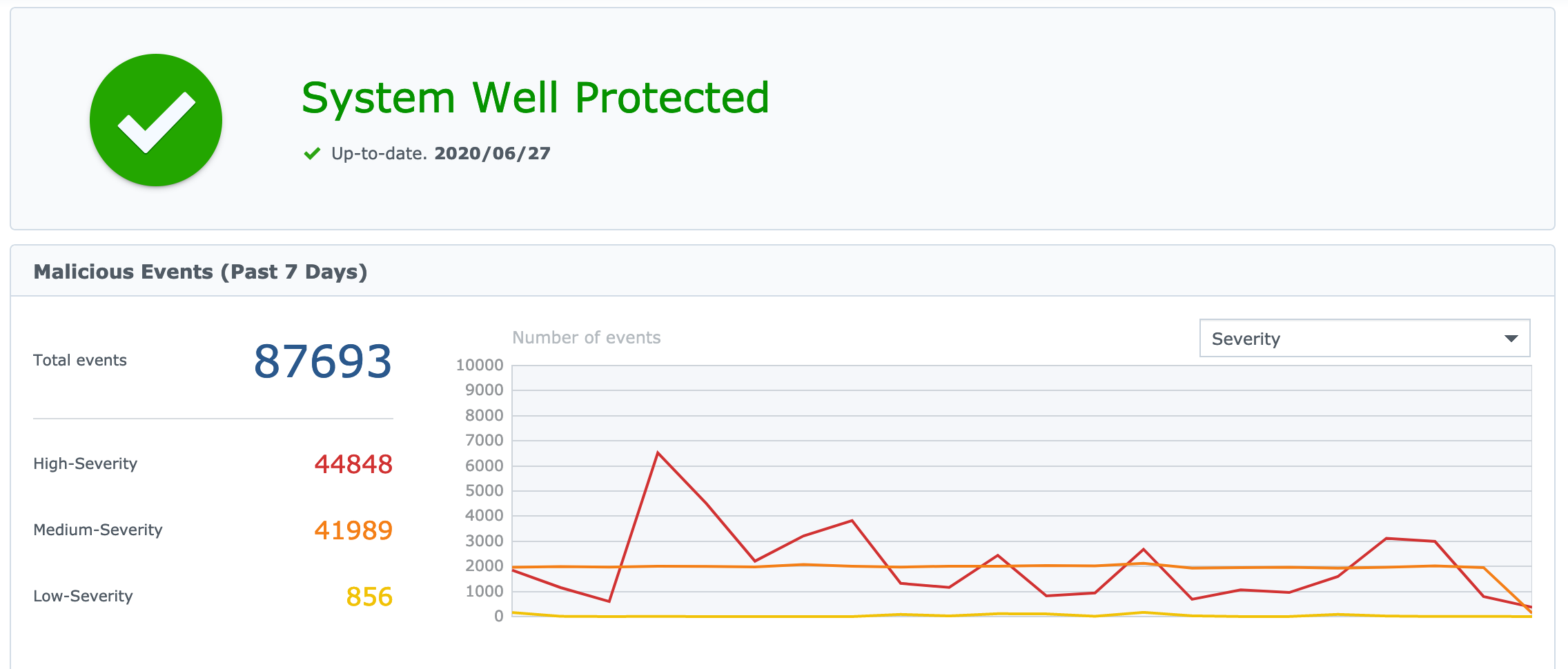
Wow! This looks like a bad situation. More high severity events than medium. The consistency of medium severity events seems odd. I have a green checkmark telling me everything is well protected. To be fair, it reports the same green checkmark even if I remove all of the alerts.
In digging deeper, the system is relying on a data feed from Proofpoint's Emerging Threats Intelligence for the definition of what's a threat or not. In reading the individual alerts and threat definitions, the high severity threats are really TURN/STUN traversal for VOIP, SIP, and video calls. The medium severity are mostly external ICMP pings or port scans. I can make the orange medium severity line spike with repeated pings from an external host.
This is trying to report on threats to the operating system and applications in my home network. What about threats to other aspects of the Internet?
Blocklists
I took Peter Lowe's blocklist converted and loaded it into the firewall. In fact, within 15 minutes, it seems loading over 3200 rules into the firewall overloaded the Qualcomm CPU within. The firewall locks up and reboots. However, while the blocklist and ET list were loaded, I did some normal browsing around the Internet.
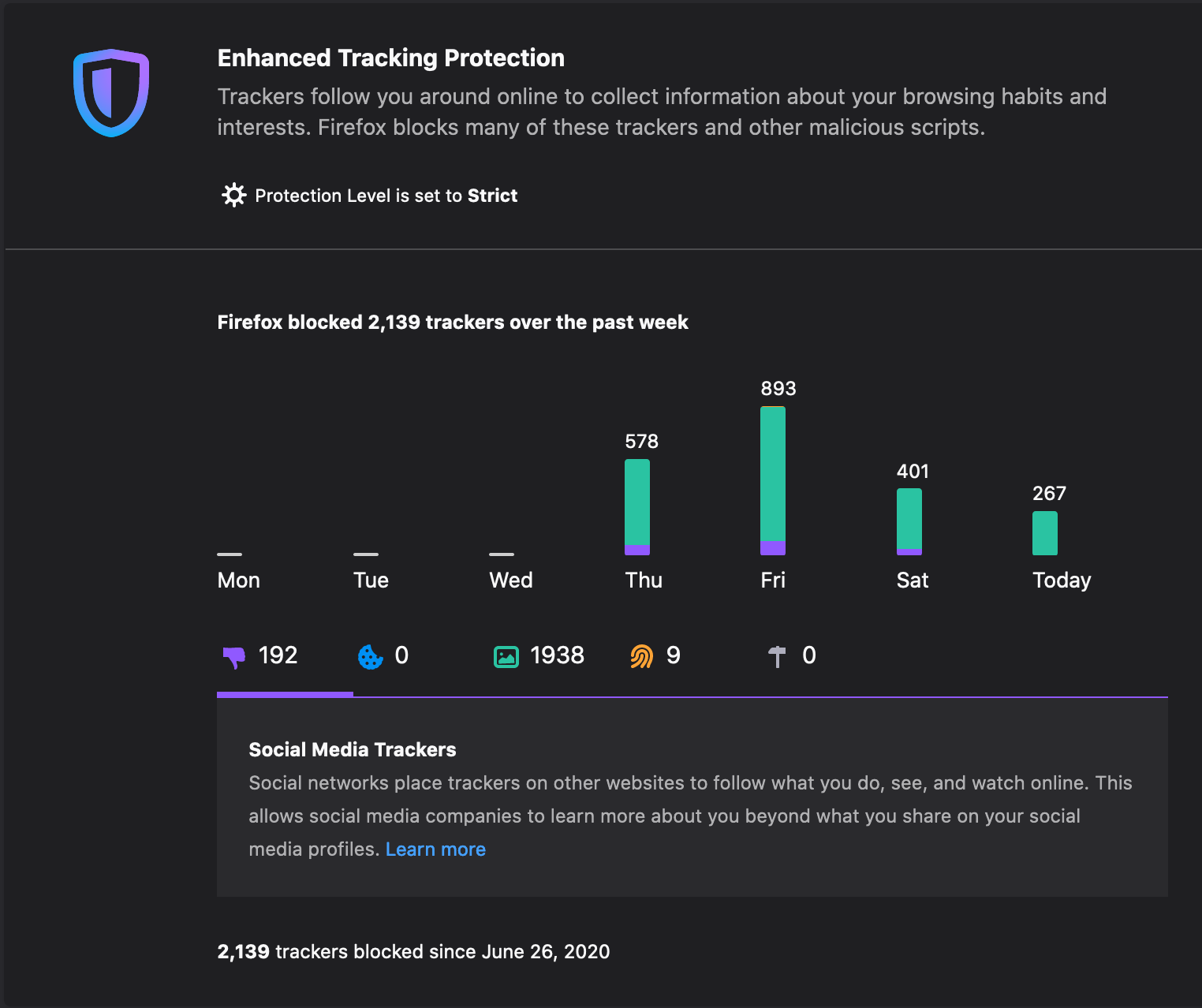
In Firefox, I loaded DuckDuckGo's Privacy Essentials and enabled "Enhanced Tracking Protection". It turns out, tracking is the real threat and not ICMP pings or TURN/STUN NAT traversal. The Peter Lowe blocklist is on the inside interface of the firewall, meaning the internal home network is firewalled from the Internet itself.
Any tracking or "privacy threats" follows this path:
my firefox -> Firefox Enhanced Tracking Protection -> DDG's Privacy Essentials -> my laptop firewall -> my home network -> external firewall with Peter Lowe blocklist and Proofpoint ET -> Internet -> requested web site.
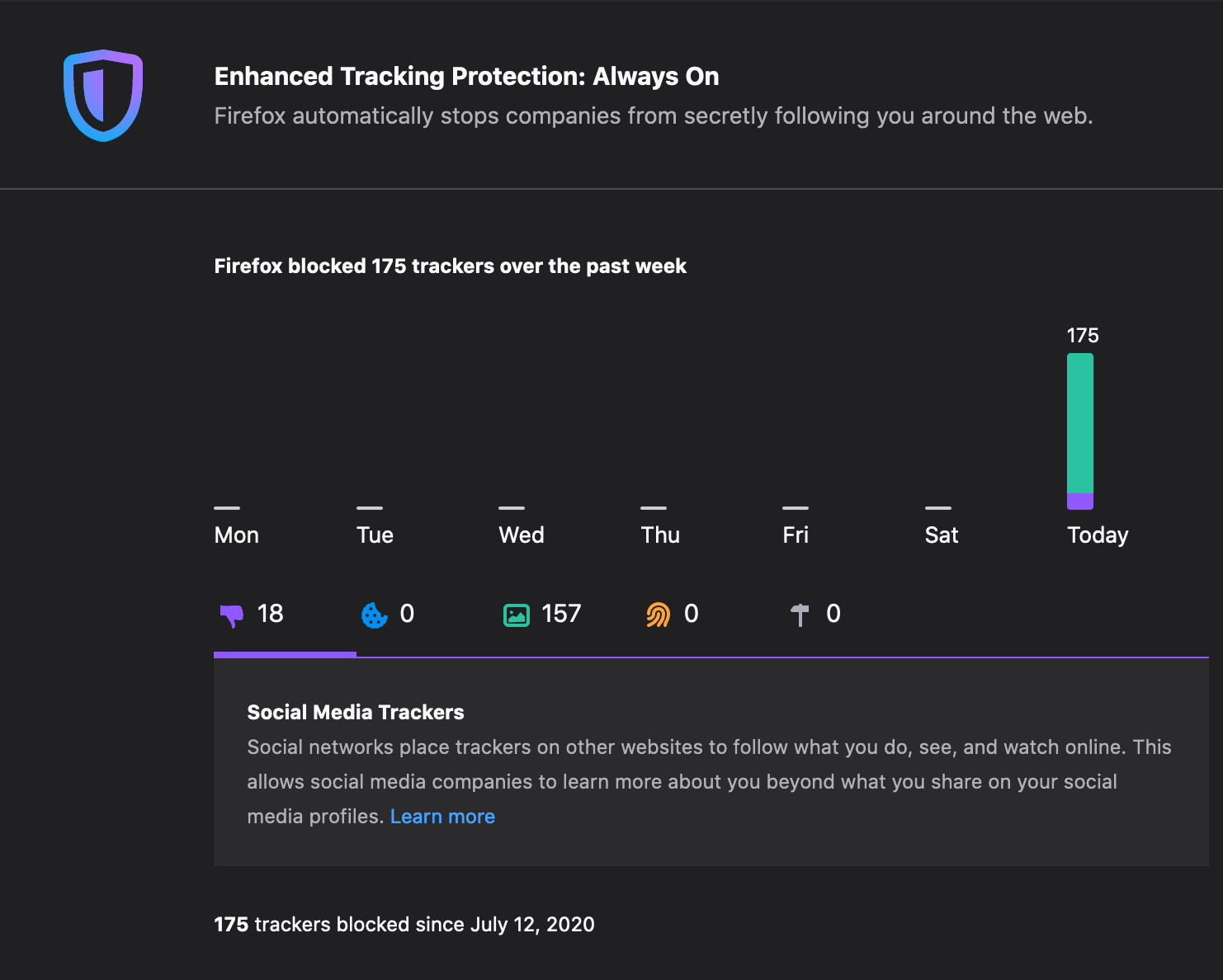
Somehow through all of that, 192 social media trackers, 1,938 content trackers, and 9 fingerprinting attempts were blocked in the browser.
Extreme Measures
Ok. Time to get extreme.
I setup a free trial of NextDNS. I enabled every option in Security, Privacy, and Parental Control. Between my local network firewall, laptop firewall, DDG PE, PFPT ET, Firefox ETP, I should be safe. I setup the home router/dhcp server to only use NextDNS for dns resolution. I loaded Peter Lowe's blocklist into my laptop firewall.
I started up my RSS feed reader and clicked on every link shown. On the one hand, an Internet full of advertising, tracking, and distraction is now mostly just content. In some ways, it's glorious. In other ways, I can't reach a ton of things. My bank website is broken, as are most sites which require a login.
Here's what this news story looks like through my NextDNS profile:
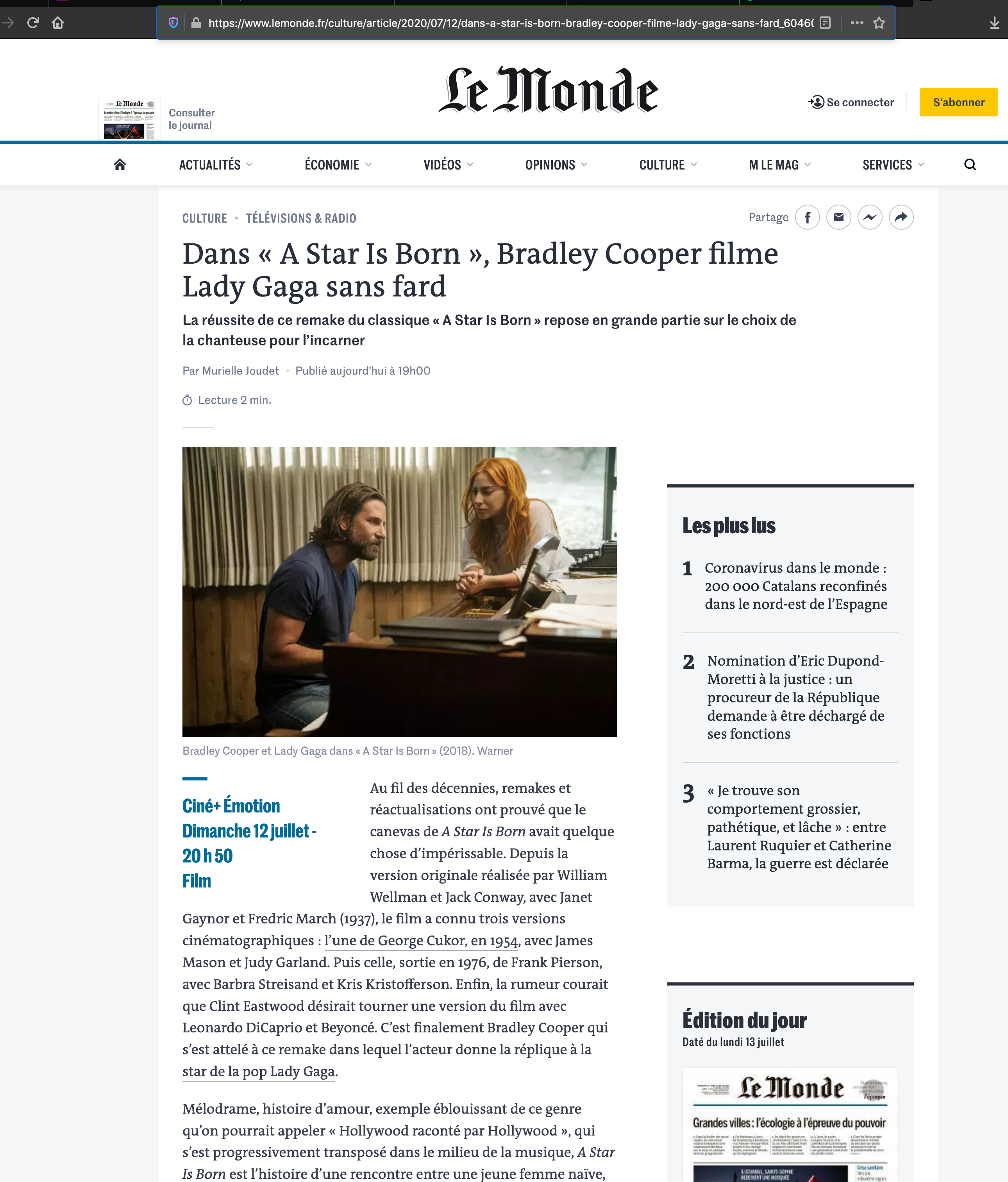
There is a lot of whitespace there. Notice how different it looks in your browser without all of the ad, tracking, and shared services links? Sites that do not rely on a ton of 3rd parties are still fairly normal looking. Take this article in Le Monde for instance:
Ahh but did you notice the Shield Icon has colors? This means Firefox is blocking something. Let's see what's blocked:
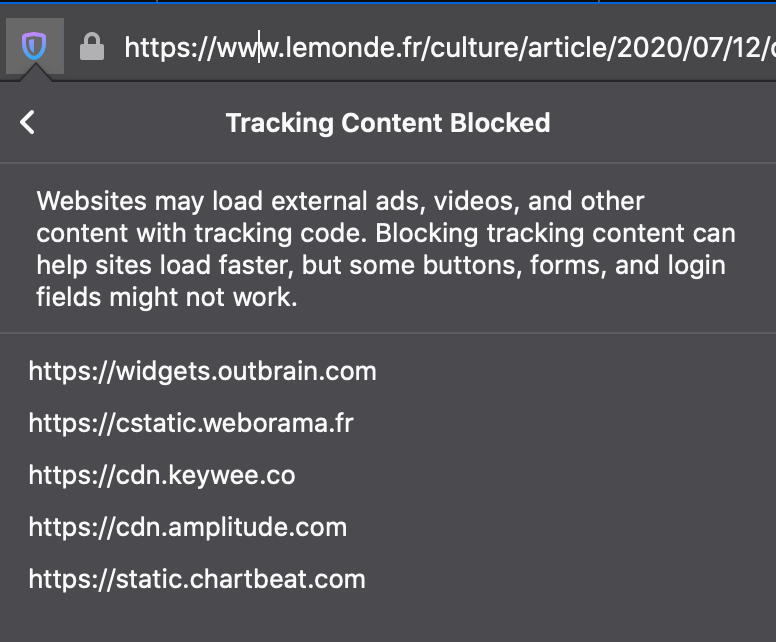
I could add those domains to NextDNS to further block them. Why they aren't already blocked in the literally over 50 blocklists? who knows!?
Just the test of the extreme setup, still shows Firefox ETP is detecting and blocking sites.
Here's what NextDNS is reporting as blocked in my 30 minute experiment.
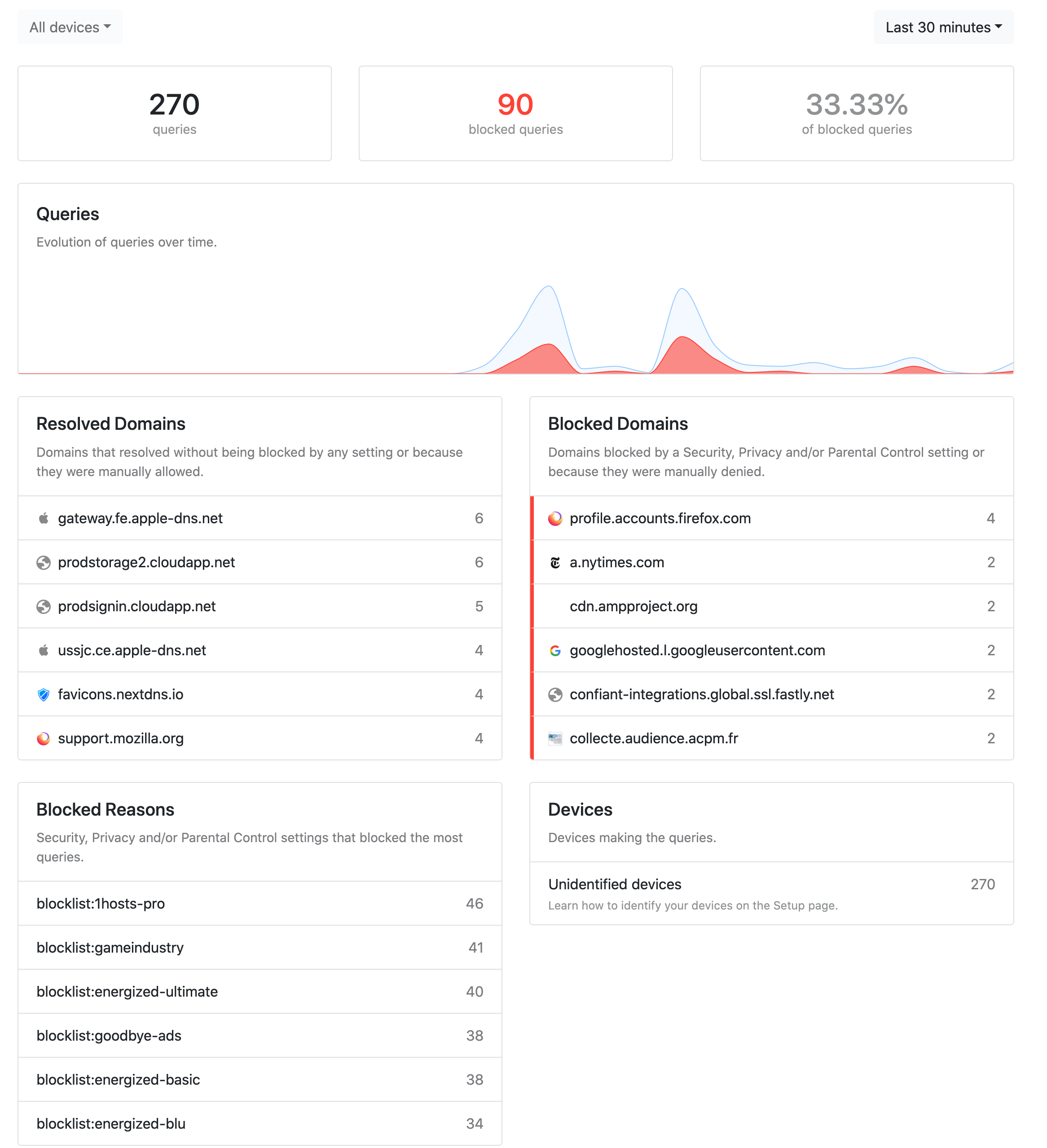
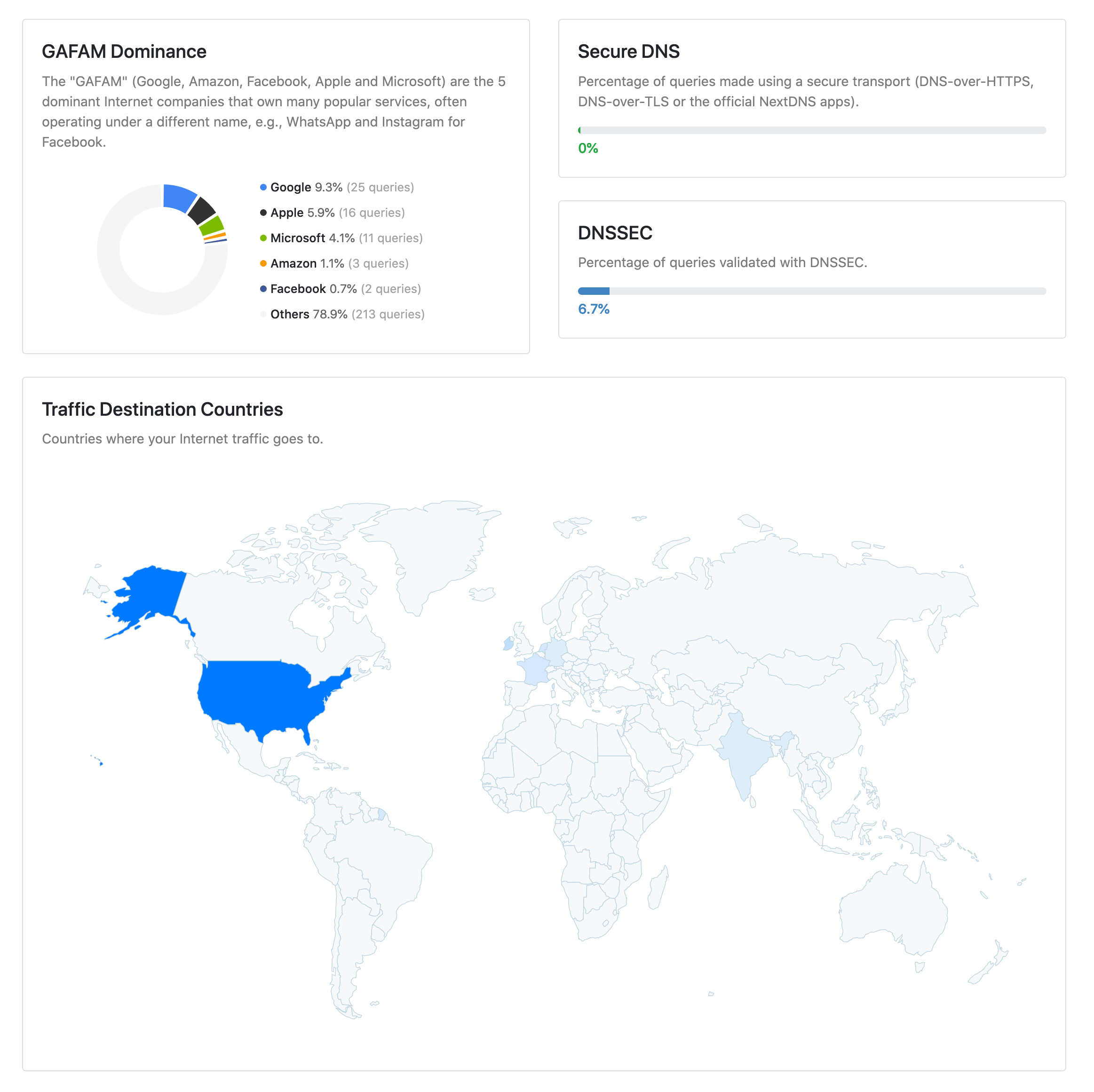
I suspect over time, privacy threats will vastly outweigh whatever the firewall PFPT ET list thinks are threats.
In the end, it turns out the most threats are those we request.