hardware (21)
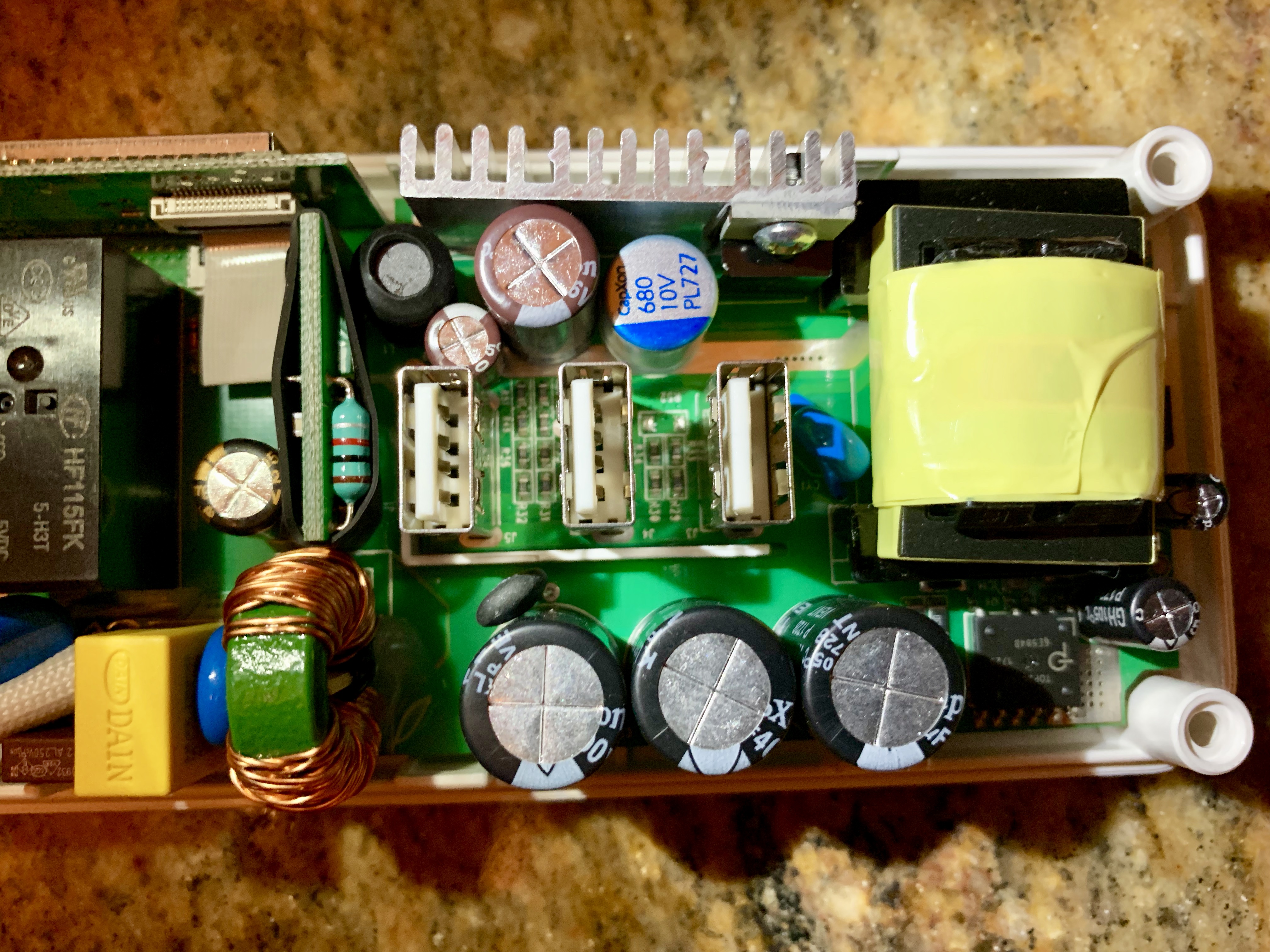
Teardown of Inseego M3000B
Another Silent, Fanless 10 Gigabit Switch

Synology Serial Console

Thinking about Secure Computing

HTC 5G Hub Teardown
High Performance lewman.com

Random Comparison of iPhone and OnePlus Cameras

ML Firearm Detector: Work in Progress
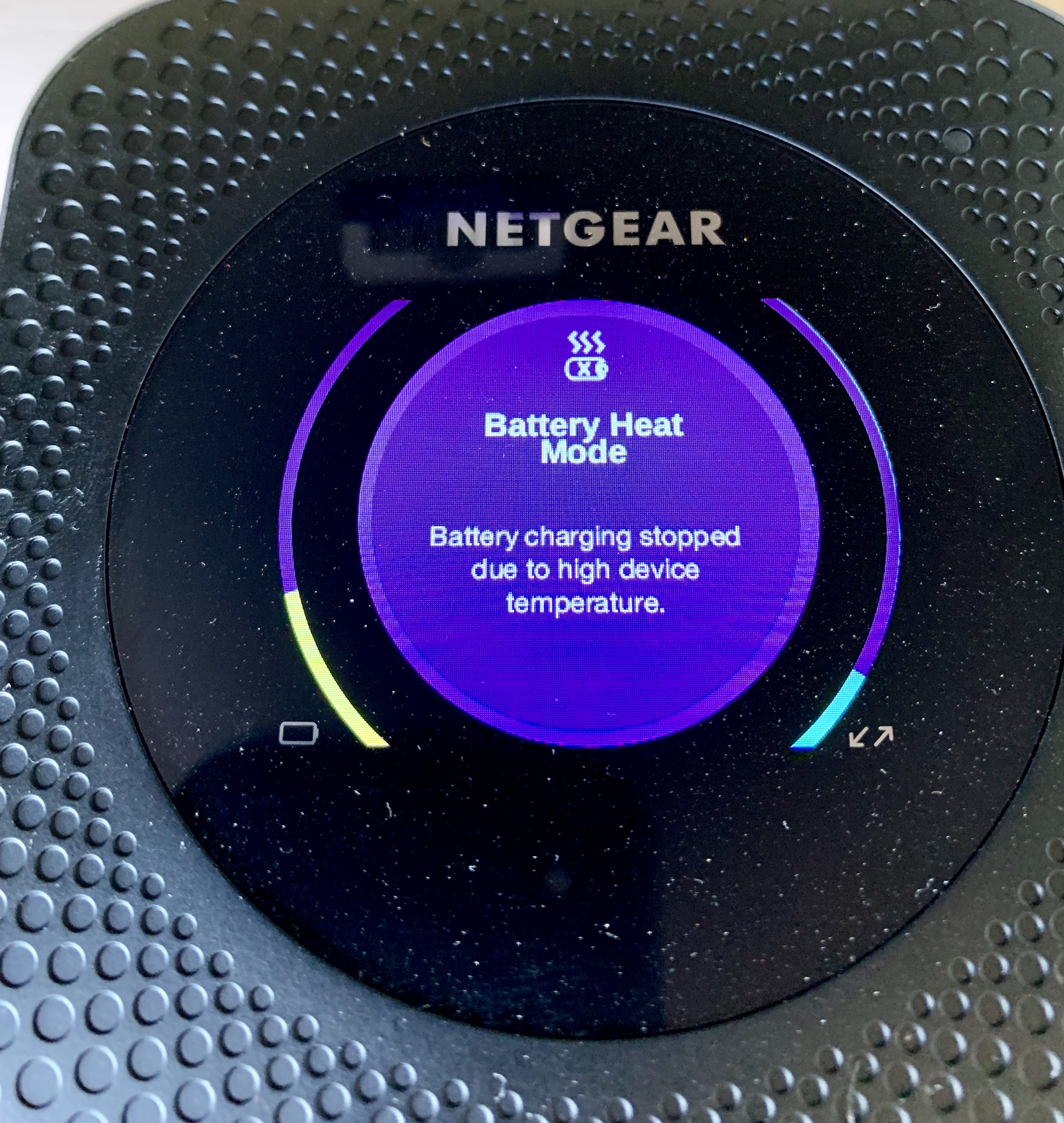
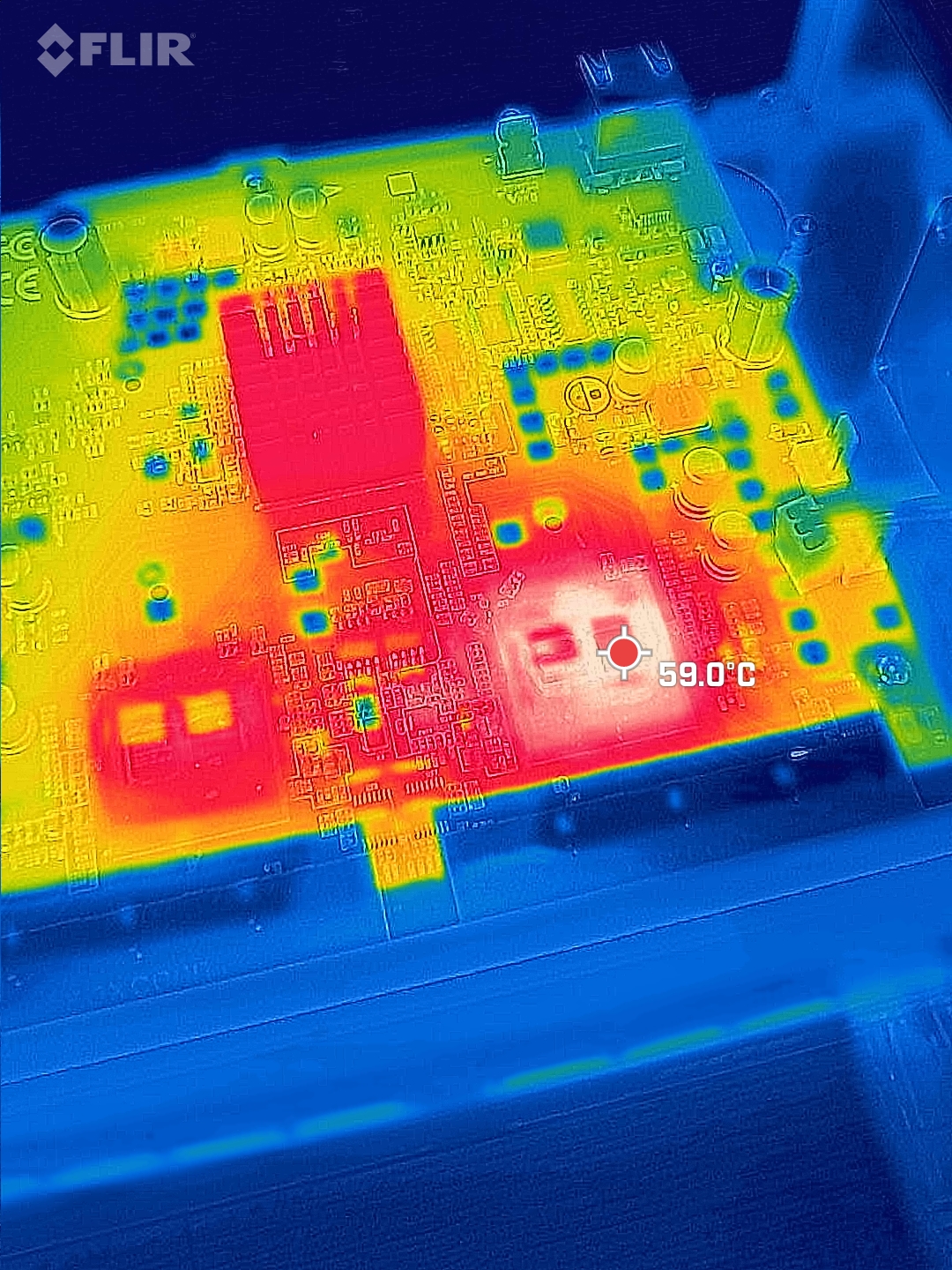
IoT in the heat